
Uses of Microsoft Intune in a Remote Work Environment
Streamline Your Remote Work Environment with Microsoft Intune
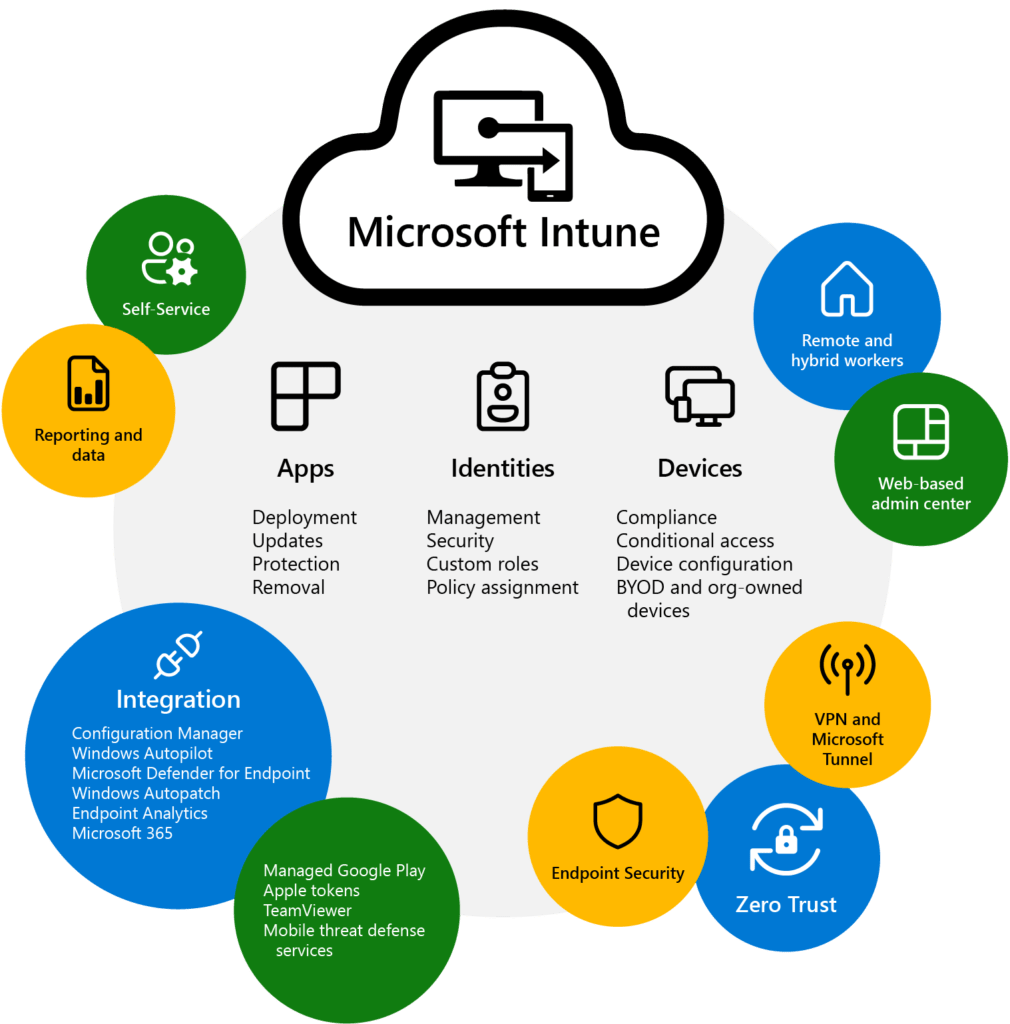
Microsoft Intune is a powerful mobile device management (MDM) solution that allows businesses to manage and secure the devices used by their employees. Intune is designed to work seamlessly with other Microsoft products such as Office 365, Azure Active Directory, and Windows 10, making it an extremely effective way to deploy equipment remotely.
One of the key benefits of Intune is its ability to manage devices remotely, including the ability to remotely wipe a lost or stolen device, lock a device, or push out software updates. This allows organizations to ensure their data is secure, even if an employee loses their device or falls into the wrong hands. Intune also allows businesses to set policies for device usage, including restrictions on which apps can be installed and the ability to remotely wipe corporate data from a device if an employee leaves the organization. This helps to protect sensitive business information and ensures that employees are using devices in a way that is compliant with company policies.
Another important feature of Intune is its ability to integrate with Azure Active Directory (AAD), which allows for secure, single sign-on access to cloud-based apps and services. This makes it easy for employees to access the tools and resources they need while also ensuring that only authorized users have access to sensitive data.
Overall, Microsoft Intune is a powerful and flexible solution that can help businesses of all sizes to manage and secure their mobile devices. Whether you need to secure corporate data on employees’ devices, manage software updates, or ensure compliance with company policies, Intune has you covered. Microsoft Intune is a comprehensive and user-friendly solution that can help businesses to manage and secure the mobile devices used by their employees. It provides robust security features, remote management capabilities, and the ability to integrate with other Microsoft services, making it a valuable tool for businesses of all sizes
Thank you for reading this post! If you enjoyed it, I encourage you to check out some of our other content on this blog. We have a range of articles on various topics that I think you’ll find interesting. Don’t forget to subscribe to our newsletter to stay updated with our latest information on Microsoft Security.

discover more
Integration Between Power Platform and SharePoint Encourages Innovation
Organizations are focusing on innovation, streamlining their processes, and delivering better experiences for employees and customers. Power Platform and SharePoint are the Microsoft products that are helping organizations focus on…
Mastering Subagents in VS Code + Copilot: How To Actually Use Them
If you’ve ever dumped a giant problem into Copilot Chat and watched the conversation slowly turn into spaghetti, subagents are the feature you’ve been waiting for. Think of subagents as…
5 Common Misconceptions About Cloud Migration: Debunking the Myths
We’ve all heard of the cloud and cloud migration. But how important is it actually for your business? Organizations are moving to the cloud for several reasons: to improve agility,…
Let’s Build Something Amazing Together
From concept to handoff, we’d love to learn more about what you are working on. Send us a message below or call us at 1-800-989-6022.




